Contrôle des Accès
Conformes aux Directives Nationales
Bénéficiez d'une solution moderne d'IAM intégrant gestion des identités et accès sécurisés aux ressources de votre système d'information.
Les défis des entreprises modernes
![]()
Directive NIS2Forte
Votée en Nov. 2022, NIS 2 entrera en vigueur en France au deuxième semestre 2024, au plus tard. NIS 2 étend son périmètre à plus de 100K organisations publiques ou privées.
L'authentification multifacteur (MFA), le contrôle d'accès au SI et la gestion des droits d'accès, sont toujours au cœur des exigences de sécurité des SI.
![]()
Authentification Renforcée
Le SSO désigne un principe d'authentification unique dans un processus de renforcement de la sécurité des accès aux ressources du système d'information. FairTrust SSO regroupe les mécanismes d'authentification forte et d'automatisation de l'authentification secondaire.
![]()
Performance
La cybersécurité est un pilier fondamental de la performance des grandes entreprises. Avec la digitalisation croissante des activités, les données sensibles, les systèmes critiques sont constamment exposés à des menaces. Une attaque réussie peut entraîner des pertes financières considérables, nuire à la réputation de l'entreprise et compromettre sa compétitivité sur le marché.
 Répondre aux exigences de sécurité
Répondre aux exigences de sécurité
Cyberattacks against public institutions and businesses are growing in frequency and sophistication, affecting companies of all sizes and industries. In response, the Council of the European Union, in collaboration with national security agencies like ANSSI in France (National Cybersecurity Agency), has established a set of cybersecurity measures. These measures are augmented at a local level by sector-specific regulations.

Directive NIS 2
Evolution du NIS 1, La directive NIS 2 s'étend aux Entités Essentielles et Entités Importantes de 18 secteurs d'activités. NIS 2 reprend les procédures de gestion des incidents, de "cyberhygiène" et toujours l'authentification Multifacteur et le contrôle d'accès aux ressources du SI
Le non respects des mesures de sécurité peut entrainer des sanctions allant jusqu'à 2% du CA mondial.

RGPD
Le règlement 2016/679 du Parlement européen et du Conseil relatif à la protection des données à caractère personnel, dit « RGPD », s’adresse à toute structure privée ou publique effectuant de la collecte et/ou du traitement de données. Il revient aux entreprises de mettre en œuvre des
mesures de sécurité adaptées aux risques sur les données personnelles. Notamment, la mise en place d’un système d’authentification fiable et robuste des utilisateurs et la définition d’une politique d’habilitation clairement définie pour limiter les accès aux données.

ISO/IEC 27001
La norme ISO/IEC 27001 fournit aux entreprises de toutes tailles et tous secteurs d’activité, des lignes directrices pour l’établissement, la mise en œuvre et l’amélioration continue de la sécurité de l’information.
Le contrôle d'accès robuste est un élément important de la norme ISO27001. Il comprend l’identification, permettant de fournir une identité reconnaissable, l’authentification visant à vérifier qu'une personne est bien celle qu'elle prétend être, les autorisations permettant de contrôler les actions qu'une personne peut effectuer sur une ressource.
En cela, l’authentification multifacteur et la gestion des droits d’accès sont des concepts importants d’une certification ISO27001.

La réglementation DORA
Le règlement 2022/2554 du Parlement européen sur la résilience opérationnelle numérique (DORA) définit des exigences uniformes pour renforcer et harmoniser la gestion des risques liés aux technologies de l'information et des systèmes d’information.
L'article 9 sur la "Protection et Prévention" impose la mise en œuvre des mécanismes d'authentification solides (MFA) et des politiques, de contrôle documenté pour la gestion des changements.
En complément, une attention particulière est portée sur la gestion des droits d'accès, la gestion des modifications et l'analyse des risques.
FairTrust IAM - Contrôle des Accès et Authentification
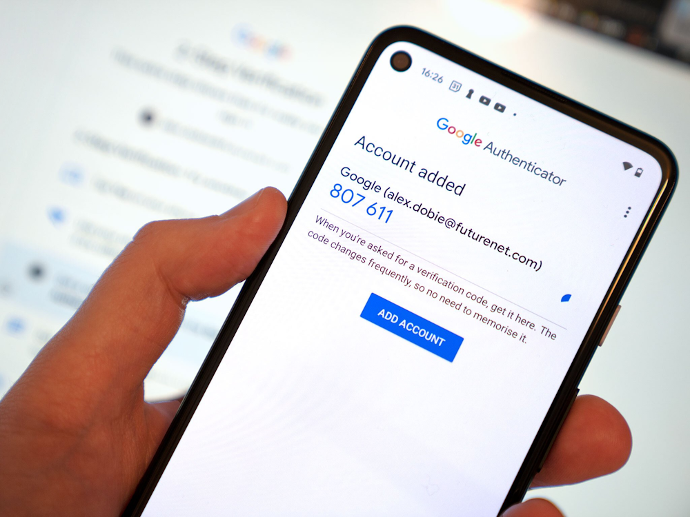
Authentification par smartphone (HOTP/TOTP)

Support des systèmes physiques homologués (principe des 3 facteurs)
Ce qu'en penses nos clients
Le retour d'expérience de Monsieur Tallot sur le choix de la solution FairTrust en réponse aux besoins de sécurisation des accès au SI, conforme aux exigences réglementaires et aux besoins des utilisateurs.
C’est un partenariat de confiance avec la R&D FairTrust,
une équipe très réactive et à l’écoute de nos besoins...

Monsieur Christophe Tallot - DSI du Groupe Mazars
![]()
Authentification automatisée
Traitez rapidement l'authentification automatisée dans toutes vos applications, gérez des mots de passe robustes d'une entropie supérieure à 50 et renouvelez les régulièrement, sans actions des utilisateurs. Associez confort et sécurité.
![]()
Authentification Forte - MFA
Support de multi systèmes d'authentification : Carte à puce, carte sans contact, clé FIDO2... , OTP, TOTP, HOTP ... empreinte digitales, référentiel tiers OIDC, SAML v2.
![]()
(R)évolution du poste Mixte
FairTrust fait cohabiter les sessions « Personnelles » et « Kiosques » sur les mêmes postes « Mixtes ». Les utilisateurs sont automatiquement connectés sur leurs sessions « Personnelles » ou « Kiosque », en fonction de leurs profils (appartenance à un groupe AD).
![]()
Contextes multi-domaines
FairTrust SSO gère un coffre-fort unique pour toutes les entités d'un groupement (filiales, partenaires, GIP...). Les données sensibles sont stockées une seule fois dans un référentiel de sécurité centralisé, sans risque de désynchronisation
![]()
Auto-dépannage des utilisateurs
Gagnez en temps et de l'argent, en mettant à disposition de vos utilisateurs une solution d'auto dépannage (oublie du mot de passe, perte du système d'authentification) simple et efficace, tout en maintenant le niveau de sécurité des accès au SI.
![]()
Traçabilité des accès et des usages.
Garder le contrôle des accès en bénéficiant d'une visibilité sur les actions et les accès de vos utilisateurs sur l'ensemble des ressources enrôlées dans la solution.
![]()
Chiffrement des données
L'ensemble des données est stocké dans un coffre-fort et chiffré par l'algorithme AES256 GCM préconisé par l'ANSSI.
Prêt à vous lancer ? Laissez-nous un message.
Vous pouvez également nous contacter par téléphone
FairTrust
9 Allée du Bois Louët
35235 Rennes
+ 33 (0)2 30 96 07 47
Vous souhaitez être informé des dernières nouvelles de FairTrust, inscrivez-vous pour recevoir nos informations avant tout le monde.
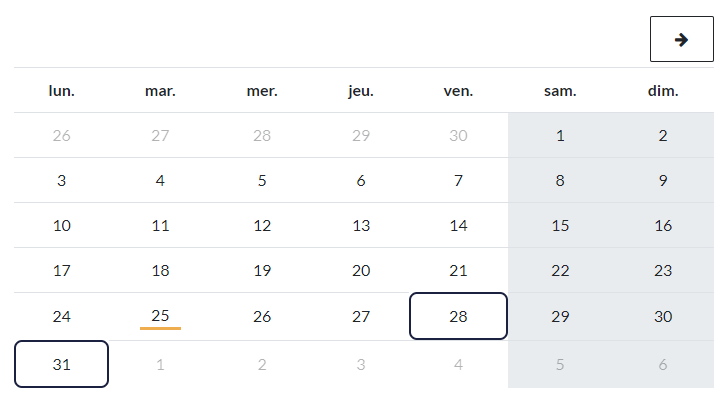
Vous pouvez également planifier directement une présentation et démonstration de nos solutions en fonction de vos disponibilités.
We are dedicated to ensuring the success of your projects.
Product Quality
Our solutions are meticulously crafted in adherence to the highest security standards and harness cutting-edge technologies to deliver exceptional performance.
Expertise in Implementation
Our solutions are deployed by our specialized partners within your industry, all of whom are certified in our products, ensuring the success of your project.
FairTrust Journey
We provide continuous support and guidance throughout the use of our solutions to ensure your satisfaction as a user on a daily basis.
Let's proceed to the next stage.
Did you know you can schedule a direct demonstration of our solutions? Let's set up an appointment and allow us to demonstrate how we can help secure your access.