Authentication & IAM
for local authorities
Ensuring Compliance with CNIL Guidelines for 'Secure and Robust User Authentication' and 'Transparent Authorization Policies' - in accordance with Regulation 2016/679 of the European Parliament and Council dated April 27, 2016, commonly known as GDPR.
Solution Globale de Gestion des Identités
et des Accès
FairTrust gère les identités des accédants au SI et restreint les accès uniquement aux ressources nécessaires et suffisantes (Approche Zéro Trust) tout en renforçant la sécurité des accès par le MFA et la gestion des mots de passe.
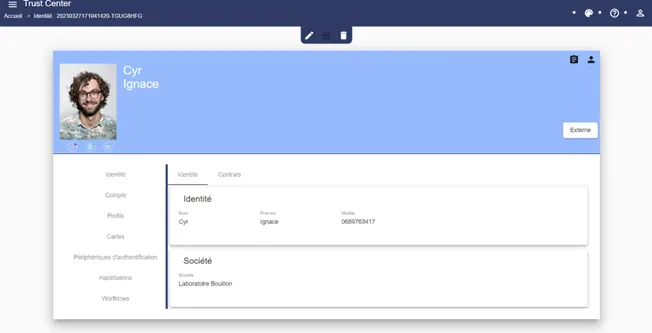
Gérer les Identités et les Droits des Accédants au SI
Assurez vous que seules les personnes autorisées puissent accéder aux ressources appropriées, selon des politiques de sécurité définies.
Renforcer la Sécurité d'Accès au SI et Automatiser l'Authentification
Assurez une traçabilité des accès, afin de minimiser les risques de compromission et améliorer l’expérience utilisateur (conformité RGPD, ISO 27001, NIS#2, DORA...).
✽ Contexte
Les Défis Sécurité SI
des Collectivités
Renforcer la Sécurité des Mots de Passe
Notamment, la CNIL insiste sur les recommandations de l'ANSSI pour l'usage de mots de passe complexes dans le respect du RGPD.
Implémenter des Coffre-Fort Numériques
L’article 87 de la loi pour une République numérique (LRN), précise que ce dernier doit garantir l’intégrité des données , tracer les opérations effectuées, garantir la confidentialité en autorisant l’accès aux seuls utilisateurs.
Gérer les Identités Respecter les Exigences Réglemantaires
Elle applique des contrôles d'accès stricts et limite l'accès aux données sensibles aux seules personnes autorisées et de réduire le risque de non-conformité. Elle permet d'implémenter une séparation appropriée des tâches (SoD).
cyber incidents from January 2022 to June 2023 in local authorities, averaging 10 incidents per month.
of incidents are related to account compromise.
the average cost of a cyberattack for an organization today.
Toutes les fonctionnalités dans 1 produit unique
Un Control Automatique des Identités
Créer automatiquement les identités numériques des accédants au SI, directement depuis vos bases RH et contrôler automatiquement "Qui" accède à "Quoi" et "Quand" ?

Automatisez la gestion des Flux de Données
Les Workflows dynamisent le traitement des processus liés à la gestion des droits et identités pour plus d'efficacité et une amélioration de l'expérience utilisateur.
Renforcement de l'Authentification
Améliorer la sécurité des accès au SI, notamment par l'implémentation de l'authentification Multi Facteur (MFA) conforme aux prérogatives ANSSI et Directives National ou Européennes de Sécurité des SI.

Report and Traceability
Gain complete, real-time visibility into identity-related activities and obtain valuable insights into resource access, permission changes, unauthorized access attempts, and other events related to identity management.
These data enable swift identification of potential security issues, detection of suspicious activities, and implementation of appropriate corrective measures.
Authentification Automatisée
Automatiser l'authentification secondaire dans toutes vos applications, soit en e-SSO, soit en passwordless, pour un accès rapide et sécurisé aux ressources SI et une amélioration de la satisfaction utilisateur
Questions fréquemment posées
Quelques questions fréquement posées sur la conformité de nos solution avec les Directives Nationales et Européennes.
FairTrust intègre l'authentification Multi Facteur (MFA) pour l'accès aux sessions de travail. L'authentification repose sur différents systèmes : Carte à puce, carte sans contact, clé FIDO2... , OTP, TOTP, HOTP ... empreinte digitales, référentiel tiers OIDC, SAML v2.
FairTrust centralise les mots de passe dans un coffre-fort sécurisé. Les identifiants et mots de passe sont facilement accessibles pour toutes les applications. En complément, FairTrust automatise les actions d'authentifications dans toutes vos applications.
Multi-Domain Context
FairTrust SSO manages a single vault for all entities within a group (subsidiaries, partners, GIP...). Sensitive data is stored only once in a centralized security repository, eliminating the risk of desynchronization.
User Self-Service
Save time and money by providing your users with a simple and effective self-service solution (password forgetfulness, loss of authentication system), while maintaining the security level of access to the information system.
L'ensemble des données stocké dans le coffre-fort est chiffré par l'algorithme AES256 GCM préconisé par l'ANSSI.
Central ID Repository
In addition, FairTrust IAM becomes your centralized directory of individuals. FairTrust IAM automates the creation of users' digital identities from various repositories and feeds your technical LDAP directories.
Automated Rights Management
FairTrust IAM automates the creation, modification, and deletion of access rights based on auditable management rules. Rights are automatically assigned according to each person's characteristics or role and their position within your organization.
Garder le contrôle des accès en bénéficiant d'une visibilité sur les actions et les accès de vos utilisateurs sur l'ensemble des ressources enrôlées dans la solution.
Vous souhaitez optimiser la sécurité des accès ?
Utilisez la solution globale IAM / SSO.
Besoin de plus d'informations?
For general purpose
FairTrust
9 Allée du Bois Louët 35235 Rennes
+ 33 (0)2 30 96 07 47
You can also schedule a presentation and demonstration of our solutions directly based on your availability.
Leave us your contact details.
En transmettant mes coordonnées, j’accepte que la société FairTrust collecte mes données afin de traiter ma demande conformément aux dispositions de traitement des données personnelles .
We are dedicated to ensuring the success of your projects.
Product Quality
Our solutions are meticulously crafted in adherence to the highest security standards and harness cutting-edge technologies to deliver exceptional performance.
Expertise in Implementation
Our solutions are deployed by our specialized partners within your industry, all of whom are certified in our products, ensuring the success of your project.
FairTrust Journey
We provide continuous support and guidance throughout the use of our solutions to ensure your satisfaction as a user on a daily basis.